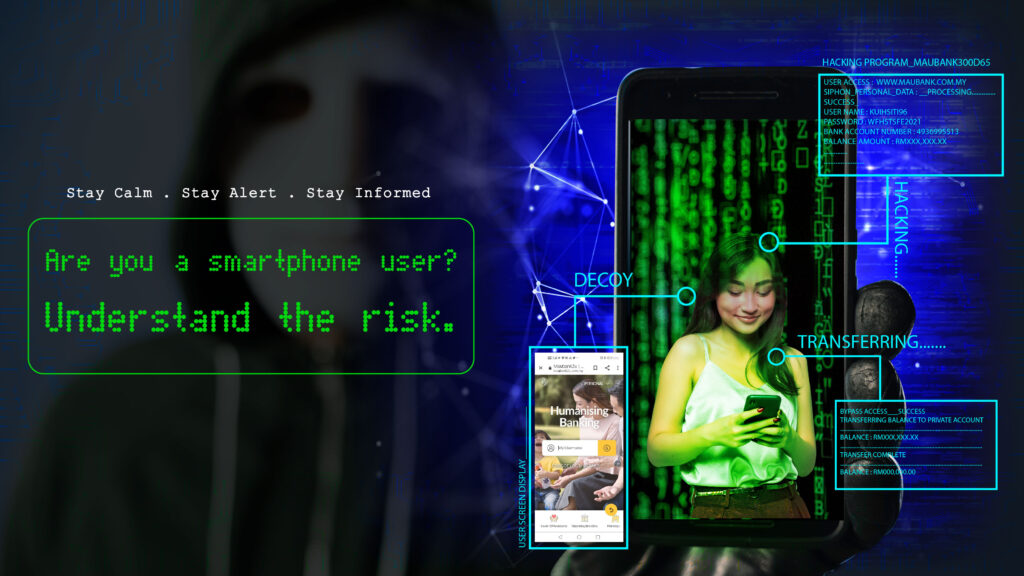
Your answer to the above question is most likely a yes. You might even be reading this article from your smartphone as of now. As in any technology, the convenience of smartphone usage comes with its own risk and danger. Some of these risk and danger is so sophisticated it simply went over your head while some others are so obvious that sometimes it draws a blank on you. Regardless, let us reminds you of these risk while also accumulating new information at the side.
The risk that comes with smartphone usage can be roughly be divided into 3 :
Phycological Risk – where smartphone user grows heavily dependent on their device for daily activities and routine to the level that can be seen as an addiction.
Physical Risk – these mobile devices are technically computers, with all kinds of your personal information inside, in a tiny form factor which increases the risk of being lost or stolen.
Digital Risk – the somewhat sophisticated risk that we are going to focus on this time around. The digital risk can be further classified into 4 vectors of risk, and 3 components of risk.
The 4 vectors of Digital risk :
- Device
- Apps
- Web
- Network
The 3 components of Digital Risk :
- Attack/Threat
- Vulnerability
- Behavioural
The 4 vectors of risk mentioned above are meant in terms of a possible approach for cyberthreats to come from and the 3 components of risk are the possible cause or exploitable window that increases the chances of a successful cyberattack. This classification will help us to better understand the risk involved in navigating the cyber world through our usage of smartphones.
The Mobile Risk Matrix created by Lookout. (https://www.lookout.com/info/mobile-risk-matrix)
The Device risk vector
The device risk of digital risk vectors is concerning a direct risk on the device system itself. In terms of the first risk component, a cyberthreat that directly damaged the device system or a cyberthreat that utilized the device system by forced rooting on Android or forced jailbreaking on iOS. This rooting and jailbreaking will gives the attacker a developer level of access which means, all the data saved in your smartphone, hidden or not, are served as a buffet for the attacker to pick. Worse, all the cutting edge hardware on your device is most likely accessible by them too. They could probably see you through your front camera while you are on your smartphone.
The device vulnerability risk component is the vulnerability within the device system itself which will usually be patched by an OS update. But the problem with vulnerability is until its existence was known and patched by the developers, it will persist and open to be utilized by attackers. Like how it was used by Pegasus Spyware, you can read a little overview about it here.
The device behaviour risk component is more onto the smartphone users themself in configuring their device system as in intentionally doing the rooting or jailbreaking, or enabling developer mode, disabling updates, and such for whatever reason. Device behaviour risk can also include user’s action when faced with cyber threats including but not limited to phishing and spoofing.
The Apps risk vector
The app threat risk component is applications that are created to automate or assist the attacker in the process of stealing data, causing damage, or providing unauthorized remote access to the targeted device. An example of this is a legitimate mobile app that was modified to infect or inject malware or malicious codes into their sister app across the network for the mentioned purpose.
Vulnerability risk in both PC software and mobile app is unavoidable. But while PC software is likeliest to be vetted by IT professionals and developed by big software companies. Most mobile apps in the market are developed by a small team of developers, possibly indie app developers, and it goes directly into the hands of end-consumer that is the smartphone users. Thus the updates and patches for bugs, glitches, poor codes quality in mobile apps can be a tad slower and becomes a big vulnerability window for cybercriminals to jump through.
The app behavioural risk component can be said to have two(2) parts. The first one is the installation of an uncertified app from an unknown source which falls under the user responsibility. The second one, the behaviour of the app itself where some legitimate apps need access to sensitive information to perform their intended functions such as health monitoring apps, online shopping apps, etc. Let’s not forget that even these apps can be compromised by the previously mentioned risk components.
The Web risk vector
The threat component of the web risk vector is very simple to understand if you have read our previous articles about Phishing and Spoofing. The spoof URL within a phishing message is very highly likely to be tapped on mobile devices compared to on PC and are more likely to fall victim to spoofing websites primarily because the URL in the message itself is probably shortened while in the browser, the URL is partially hidden because of screen limitation. Not to mention some spoof websites can automatically download malicious code or malware onto your mobile device while appearing harmless.
A well-known web vulnerability is called Stagefright where .mp3 and .mp4 formatted files from a visited website have direct access to the media processing library on Android which could be exploited in many ways. Another example is when the previously mentioned Pegasus Spyware utilized a vulnerability in Safari for iOS, before it being patched, to deliver the spyware payload.
The third risk component is regarding the user’s browser settings and configurations (media auto-play for example), visiting websites that didn’t properly encrypt credentials, clicking URL or media links in suspicious email or messages or even on ambiguous websites. All this can be classified under the behavioural component of the web risk vector.
The Network risk vector
Simply speaking, the network risk threat component is the cyber attack that could occur over the mobile device network connection. These attacks could be done directly by the attacker or by malware, over both wifi or cellular network. Some examples of these threats include man-in-the-middle attacks (MITM), certificate impersonation, SSL/TLS striping, and SSL/TLS cypher suites downgrades.
Network vulnerabilities risk factor could either be on the software or hardware flaws on the network interface of the device as in the device OS network driver. Before patch 10.3.1 is released, iOS devices have a network vulnerability that could allow arbitrary code execution over the wifi network.
Network behavioural risk component could be best represented by smartphone users connecting to publicly available Wi-Fi networks as in coffee shops, hotels, airports, which could lead the user to non-encrypted access to the internet. These careless choices could end up in a number of cyber attacks as mentioned above.
Smartphone users need to be smart too
At the end of the day, a smartphone is nothing but a tool regardless of how smart a device it is. It will always be human user choices and decisions that greatly affect the end results. And to make correct decisions, you will be needing proper knowledge and correct information. Follow our Facebook Page to get constantly updated about Cyber Security and be the first to know of our latest posting. Look forward to our live stream where we will be showing you the hands-on example of Cyber Attack occurrence.